How secure are public wifi networks really?
It is midday on a Tuesday and I am sat sipping a latte in my work clothes, with my MacBook on the table in front of me. I’m working from a coffee shop located in the centre of Leeds, which is surrounded by busy offices filled with solicitors, bankers, ecommerce companies and public sector organisations. As usual, people start rushing into the coffee shop for a short break in their working day, to grab a drink and a bite to eat.
The majority of them are on their mobile phones and laptops, some having working lunches with laptops, and some just browsing the internet on their electronic devices. They are all here for different reasons but the majority of them have one thing in common: they are all using the same Wi-Fi network, provided by the coffee shop as an incentive. Lovely! Time to begin…
Wondering what’s lovely? Because all of these people are connected to the Wi-Fi network, I am now able to “grab” what’s in the air, and see what the majority of people are looking at on the internet.
I spent an hour simply capturing the Wi-Fi signals in the coffee shop to see what I could discover for this article. During this time about 85 per cent of all the traffic that came from laptops was unprotected (so I could see exactly which websites they were visiting) and over 72 per cent of the mobile traffic was the same.
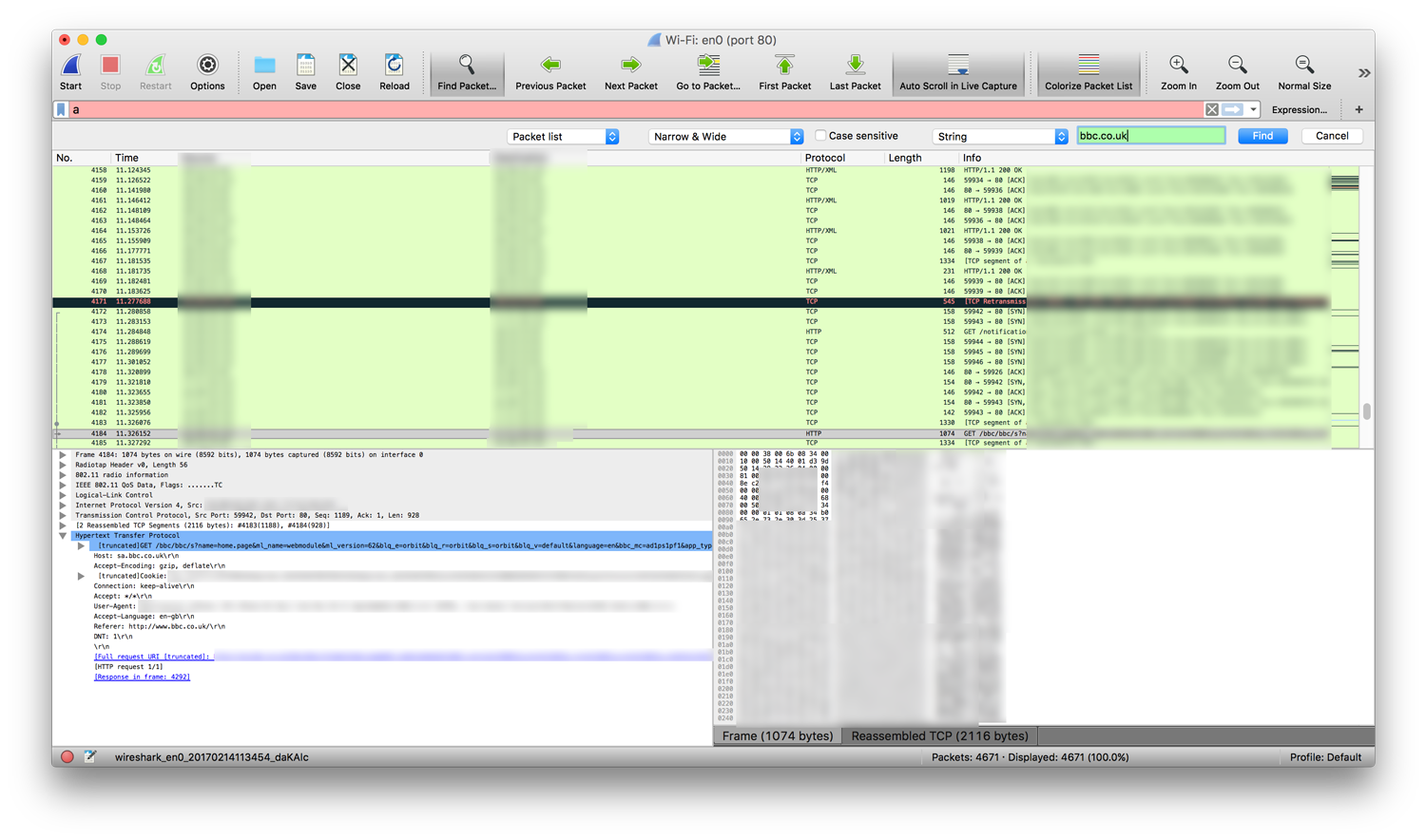
The majority of this traffic was useless to me for this study, with people visiting sites such as the BBC, LadBible and Mashable.
However, 2 per cent of this traffic was valuable to me, well it would be if I were a hacker. It contained sensitive information that I could be used for untoward means, including emails, visits to important websites, passwords and other personal information.
The average Wi-Fi user has got no idea that it is possible for me (and others) to access this information. In fact, I’d go as far as to claim that a large number of people who work within the IT and digital sector won’t know that this is possible and I do not blame them for not knowing – it is not their speciality. Sadly, this is also the case for most web developers.
Although software development culture has been around for a few decades, we have gone through many iterative changes, from highly secure and controlled environments to fast moving environments to speed up production.
As a result, a whole spectrum of professionals and not-so-professionals have come out of it. Some of them just like the builders that you see on Cowboy Builders, and some who can expertly and successfully plan and build sky scrapers which will last for centuries to come.
I only spent an hour in the coffee shop today, and it was shocking to learn that the majority of websites that customers were visiting weren’t making the basic attempts to protect their visitors. What shocked me further was the fact that I saw somebody visiting the website of one of the UK’s biggest law firm’s to fill in their personal information, which I could then simply captured. We should be able to trust law firms and yet they do not take the privacy of potential clients seriously. I informed this particular law firm of the issue, but they just stated, “We have a security certificate so we are ok”, without taking any further action.
Now, if I was to sit in the coffee shop for several days in a row during busy periods, or perhaps even just place a Raspberry Pi in there for a few weeks, I could have collected hundreds and thousands of pieces of private data – that could be emails, personal photographs, confidential information, and perhaps login details to important websites. Owners and developers of these websites need to take action to protect their visitors and themselves.
Over the next few months I will be writing up a series of articles covering what consumers need to look out for, and what website owners need to do to make sure that their developers take the right action.
These articles will also include ways to help developers improve their security knowledge, covering basic security topics such as SSL and also more advanced methods of website security improvement such as WAF and protecting yourself against OWASP Top Ten.
This series will conclude with an article where I will attempt to uncover a flaw or potentially big security issue within the website of one or more large UK corporations. After all, these security breaches could affect you, me, or anyone.